BCR Cyber offers comprehensive IT/cyber training programs designed to equip individuals with the skills and knowledge needed to excel in the field.
We take pride in our diverse range of training programs tailored to meet the unique needs of our clients.
Whether you are an aspiring IT professional, a cybersecurity enthusiast, or an organization/government entity seeking to enhance your workforce’s capabilities, we have the right program for you.
1. Entry-Level Training: Our entry-level training program is designed for individuals who are new to the industry or looking to transition into IT/cyber careers. We provide a solid foundation of knowledge and skills to help you kickstart your journey in this dynamic field.
2. Journeyman Training: Our journeyman training program is specifically designed for individuals with intermediate-level experience in cybersecurity. This program focuses on further advancing your skills and expertise, allowing you to take your career to the next level. We offer specialized courses and hands-on training to deepen your understanding of advanced cybersecurity concepts and techniques.
3. Advanced Training: Our advanced training program is tailored for experienced professionals seeking to enhance their expertise and stay at the forefront of the rapidly evolving cybersecurity landscape. We provide cutting-edge courses and specialized training to help you tackle complex cybersecurity challenges and lead in your field.
We understand that each organization has unique training requirements. That’s why we also offer customized training programs tailored to address your specific needs. Our team of expert trainers will work closely with you to develop a program that aligns with your organization’s goals and challenges.
At BCR Cyber, we believe in a hands-on, practical approach to training. Our programs combine theoretical knowledge with real-world scenarios, enabling participants to apply their learning to practical situations. Through interactive exercises, simulations, and case studies, we ensure that our training is engaging, immersive, and highly effective.
To accommodate different learning preferences and circumstances, we offer both remote and in-person training options. Our remote training allows you to access high-quality instruction from anywhere, while our in-person training provides a collaborative and immersive learning experience at our state-of-the-art training facility.
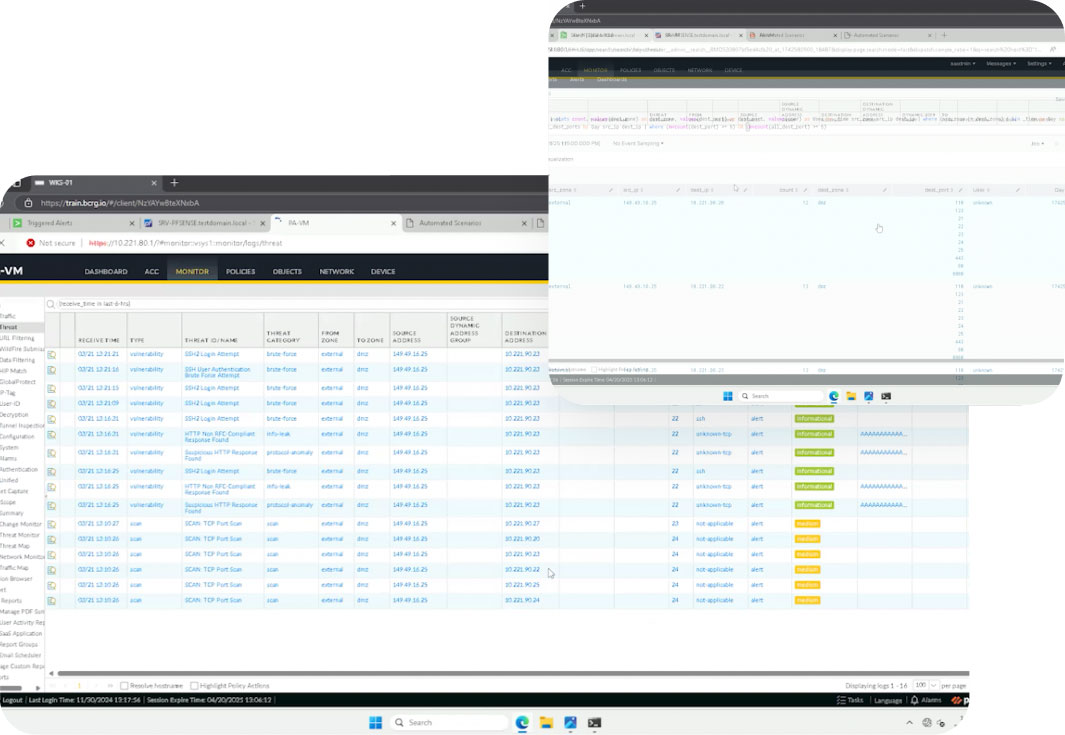
Range Simulation
A hands-on, practical approach to training.
Our programs combine theoretical knowledge with real-world scenarios, enabling participants to apply their learning to practical situations. Through interactive exercises, simulations, and case studies, we ensure that our training is engaging, immersive, and highly effective.
To accommodate different learning preferences and circumstances, we offer both remote and in-person training options. Our remote training allows you to access high-quality instruction from anywhere, while our in-person training provides a collaborative and immersive learning experience at our state-of-the-art training facility.
The cyber range training system represents a hands-on, holistic approach to cyber training.
The training flow can be divided to three main steps each part of the integrated Training Management System:
1. Training Setup: In this stage the trainer defines the training structure, taking into consideration its goals and the skills of the trainees. The relevant cyber-attack scenarios are selected. The selected network is then automatically cloned and allocated for each scenario.
2. Training Execution: In this stage the trainer defines the training structure, taking into consideration its goals and the skills of the trainees. The relevant cyber-attack scenarios are selected. The selected network is then automatically cloned and allocated for each scenario.
3. Training Review: At this point the trainer debriefs the trainees by reviewing their performance during the training session and analyzing the attack. The training session is concluded with group and individual feedback, a summary of lessons learned and emphasis on improvement.
Workforce Development
BCR Cyber Programs
The Cyber Workforce Accelerator (CWA)™ Workforce Development (WFD) Program
The CWA features a robust Workforce Development (WFD) program built around BCR Cyber’s SOC Operations Analyst I (SOCOA I) training and certification — an Industry-Recognized Credential (IRC) designed to fast-track jobseekers into cybersecurity roles. Fully funded to train 1,100 Marylanders at no cost to participants, the WFD program is removing barriers and opening doors to high-demand careers.
And it’s all delivered virtually.
- Part I – Asynchronous Training – 40 Hours: Foundational cybersecurity instruction focused on enterprise governance, threat analysis, networking, Linux command line, and attacker behavior.
- Part II – Experiential Range Training – 8 Hours: Collaborative, instructor-led exercises on the BCR Cyber Series 3000 Cyber Range where participants detect, mitigate, and remediate simulated attacks.
- Certification Exam: A rigorous 100-question, 90-minute test measuring technical and operational proficiency.
Intrusion Countermeasures Education & Training (ICE-T)
- Maryland Department of Labor’s Employment Advancement Right Now (EARN) Program
- U.S. Department of Agriculture’s Supplemental Nutrition Assistance Program’s Education and Training (SNAP E&T) Program
Cybersecurity Operational Methods Education and Training (COMET)
The Cybersecurity Operational Methods Education and Training (COMET) was established to provide relevant, up-to-date training to state and local government employees to elevate the ability of the workforce to identify and respond to the largest cybersecurity challenges facing the state and local government. COMET training focuses on two subsets of the state workforce: Incumbent and Advanced Incumbent.
Eligibility requirements:
- Must be either a State of Maryland or Maryland Local Government Employee
- Must have at least one year of IT and/or cyber experience
- Must receive manager approval to take training during business hours
- Must be 18 years of age or older
Training & Certification
BCR Cyber Training
Governance, Risk, and Compliance (GRC) Fundamentals Training & Certification
This is an entry-level course designed to introduce participants to the principles, processes, and frameworks of IT/cyber governance. Participants gain a foundational understanding of how organizations align IT with business goals, manage resources, address risk, ensure compliance, and establish accountability across the enterprise. The course includes 8 hours of incident response & governance reporting on the cyber range in a live, simulated environment.
- Introduction to IT Governance
- IT Governance Processes I
- IT Governance Processes II
- Regulatory Compliance & Legal Considerations
- IT Governance Frameworks
- Introduction to NIST SP 800
- NIST SP 800-53 Security & Privacy Controls
- NIST SP 800-115 Testing & Assessment
- Security Assessment Planning
- Technical Writing
Fundamentals of Artificial Intelligence in Cybersecurity (FAIC)
This virtual course aims to complete and pass the FAIC exam. Participants will be better prepared to use AI and understand Machine Learning (ML), troubleshoot, problem-solve, and understand various issues that occur across the various kinds of AI and Large Language Models (LLM).
- History and Fundamentals of AI and ML
- AI in Cybersecurity
- Best Practices for AI Modeling and ML
- Foundations of Neural Networks
- Generative AI
- AI in Action
SOCOA I Training & Certification
This is an Industry Recognized Credential (IRC) and prepares learners for entry-level positions in Security Operations Centers (SOCs). Through a combination of technical instruction and immersive, hands-on experience, participants build the real-world skills from threat analysis and enterprise security to live incident response.
The training and certification includes:
- Part I – Asynchronous Training – 40 Hours: Foundational cybersecurity instruction focused on enterprise governance, threat analysis, networking, Linux command line, and attacker behavior.
- Part II – Experiential Range Training – 8 Hours: Collaborative, instructor-led exercises on the BCR Cyber Series 3000 Cyber Range where participants detect, mitigate, and remediate simulated attacks.
Work Readiness & Job Search
Strategies Training
This course is designed to prepare participants for successful entry into the IT and cybersecurity workforce by building essential professional, job-search, and career-readiness skills. Participants learn how to identify and articulate transferable skills, develop industry-ready résumés and LinkedIn profiles, prepare for technical and behavioral interviews, and effectively network with employers. The training emphasizes real-world readiness, confidence building, and practical tools to help participants stand out and secure employment in competitive technology roles.
Key Topics Include:
- Career Pathways in IT & Cybersecurity
- Identifying Transferable & Technical Skills
- Résumé & Cover Letter Development
- LinkedIn Optimization & Personal Branding
- Job Search Strategies for IT & Cyber Roles
- Networking (In-Person & Online)
- Interview Preparation & Mock Interviews
- Professional Workplace Readiness & On-the-Job Success
Certifications
Training programs that lead to industry-recognized certifications.
We offer training programs that lead to industry-recognized certifications, including but not limited to CompTIA’s A+, Network+, Security+, (ISC)2’s CISSP, Cybersecurity Maturity Model Certification (CMMC), Amazon’s AWS Certified Cloud Practitioner (CCP), and more. These certifications validate the participants’ expertise and enhance their professional credibility in the industry. BCR Cyber is a Licensed Training Provider of (ISC)2 and an Official Training Partner of the Cyber AB.
